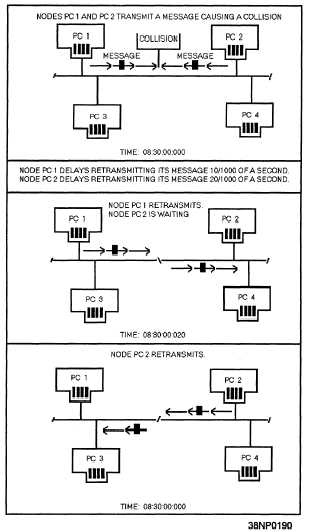
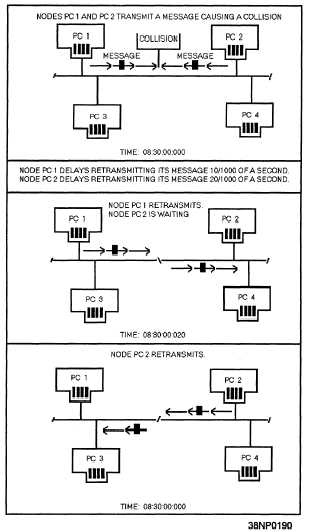
Figure 6-6.—A bus network using the CSMA/CD access
method.
arrangements used to make sure each workstation has
fair and equal access to the network. The access
method used is governed primarily by the topology
and the protocol of the network. The principal access
methods are contention and token passing.
Contention
The contention method features Carrier Sense
Multiple Access (CSMA) and Carrier Sense Multiple
Access with Collision Detection (CSMA/CD). The
CSMA/CD method is shown in figure 6-6. Access for
both is on a first-come, first-served basis. The CSMA
access scheme is very similar to that of a citizens band
(CB) radio. Stations with data to send listen to the
channel and wait until it is clear to transmit. With
CSMA/CD, when two or more workstations transmit
simultaneously, their messages will collide. As soon
as a workstation detects a collision, it ceases
transmission, monitors the network until it hears no
other traffic, and then retransmits. Most contention
networks assign a unique retry algorithm to vary the
wait-and-retry period.
This algorithm reduces the
likelihood that after a collision, two workstations will
transmit retries simultaneously.
Token Passing
Token passing is an orderly access method and is
shown in figure 6-7. Each workstation passes on the
opportunity to transmit to its closest neighbor until a
station is found with a message to send.
This
permission to transmit is called a token. When a
workstation with data to send is handed a token, part
of the token is changed, indicating it is carrying a
message, and then data is transmitted with the token.
The token is then passed around the network, and
every station checks whether the message is intended
for it. The receiving station copies the message from
the token, but then passes the unchanged token along
the network. When the transmitting station receives
the same token, it knows the message has been passed
around the network. The transmitting station erases
the message and puts the empty token back into
circulation on the network.
The amount of
information that maybe transmitted during possession
of the token is limited so that all workstations can
share the cable equally.
PROTOCOLS
Network protocols are an important component
because they define how networks establish
communications
between elements, exchange
information,
and
terminate
communications.
Protocols have two major operational functions. They
establish the circuit for transmission (handshaking)
and for the transmission itself. Transmission is
conducted subject to the line discipline. The line
discipline is the sequence of operations that actually
transmits and receives the data, handles the
error-control procedures, handles the sequencing of
message blocks, and provides for validation for
information received correctly.
6-10